What Is DHCP Snooping?
The Dynamic Host Configuration Protocol (DHCP) snooping feature ensures that DHCP clients obtain IP addresses only from authorized DHCP servers and a DHCP snooping-enabled device records mappings between IP addresses and MAC addresses of DHCP clients, preventing DHCP attacks on the network.
Why Do We Need DHCP Snooping?
DHCP defined in RFC 2131 is susceptible to certain attacks, such as a bogus DHCP server attack, DHCP server DoS attack, and bogus DHCP message attack.
DHCP snooping functions as a firewall between DHCP clients and the DHCP server to prevent DHCP attacks on the network, facilitating security for communication services.
What Are Application Scenarios of DHCP Snooping?
Defense Against Bogus DHCP Server Attacks
Mechanism
Because DHCP servers and DHCP clients lack authentication mechanisms between them, each DHCP server newly configured on a network assigns IP addresses and other network parameters to DHCP clients. If the assigned IP addresses and other network parameters are incorrect, errors may occur on the network.
In the following figure, authorized and unauthorized DHCP servers can receive DHCP Discover messages broadcast by DHCP clients.
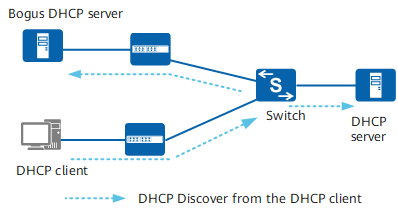
DHCP client sending DHCP Discover messages
If a bogus DHCP server sends a bogus DHCP Reply message with an incorrect gateway address, Domain Name System (DNS) server address, or IP address to a DHCP client, as shown in the following figure, the DHCP client cannot obtain the correct IP address and required information. The authorized user then fails to access the network and user information security is compromised.
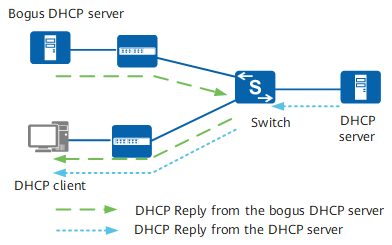
Bogus DHCP server attack
Solution
To prevent attacks from a bogus DHCP server, configure the trusted interface and untrusted interfaces on the device.
You can configure the interface directly or indirectly connected to the authorized DHCP server as the trusted interface and other interfaces as untrusted interfaces. The device then discards DHCP Reply messages received on untrusted interfaces, preventing bogus DHCP server attacks, as shown in the following figure.
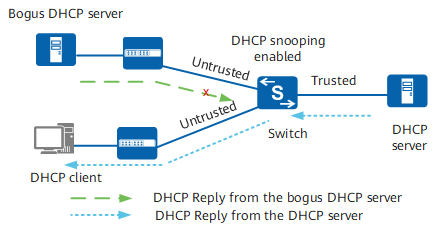
Trusted interface and untrusted interfaces
Defense Against Attacks from Non-DHCP Users
Mechanism
On a DHCP network, users with static IP addresses may initiate attacks such as bogus DHCP server attacks and bogus DHCP Request message attacks. This brings security risks for authorized DHCP users.
Solution
To prevent attacks from non-DHCP users, enable the device to generate static MAC address entries based on the DHCP snooping binding table, and disable the interface from learning dynamic MAC address entries. Only the messages whose source MAC addresses match the static MAC address entries can pass through the user-side interface on the device, and other messages are discarded. To allow messages from non-DHCP users to pass through the interface, manually configure static MAC address entries for these users.
The device learns and generates dynamic MAC address entries, whereas static MAC address entries are configured using the CLI. A MAC address entry includes the MAC address, VLAN ID, and interface number of the DHCP client. The device implements Layer 2 forwarding based on MAC address entries.
Defense Against DHCP Flood Attacks
Mechanism
On a DHCP network, if a large number of DHCP messages are sent to the device within a short period of time, device performance may deteriorate, preventing the device from working properly. This kind of attack is known as a DHCP flood attack.
Solution
To prevent DHCP flood attacks, enable DHCP snooping and enable the device to check the rate at which DHCP messages are sent to the processing unit. The device then limits the rate at which it sends DHCP messages to the processing unit and discards those that exceed the rate.
Defense Against Bogus DHCP Message Attacks
Mechanism
An authorized DHCP client that has obtained an IP address sends a DHCP Request message or Release message to extend the lease time or to release the IP address. If an attacker continuously sends DHCP Request messages to the DHCP server to extend the lease time, the IP address cannot be reclaimed or obtained by authorized users. If an attacker sends forged DHCP Release messages to the DHCP server, the authorized user may be disconnected.
Solution
To prevent bogus DHCP message attacks, use the DHCP snooping binding table. The device checks DHCP Request messages and Release messages against binding entries to determine whether the messages are valid. Specifically, the device checks whether the VLAN IDs, IP addresses, MAC addresses, and interface IDs in DHCP messages match binding entries. If a message matches a binding entry, the device forwards the message. Otherwise, the device discards the message.
Defense Against DHCP Server DoS Attacks
Mechanism
In the following figure, if a large number of attackers request IP addresses on if1, IP addresses in the IP address pool are exhausted. This results in no IP addresses being available for authorized users.
A DHCP server identifies the MAC address of a client based on the client hardware address (CHADDR) field in the DHCP Request message. If an attacker continuously applies for IP addresses by changing the value of the CHADDR field, IP addresses in the address pool on the DHCP server may be exhausted. As a result, authorized users cannot obtain IP addresses.
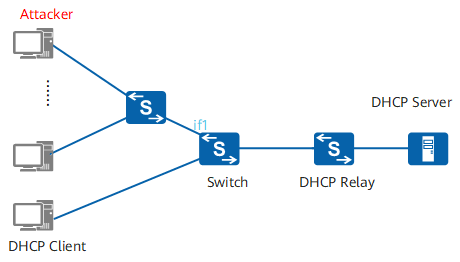
Defense against DHCP server DoS attacks
Solution
To prevent DHCP server DoS attacks, enable DHCP snooping on the device and then set the maximum number of access DHCP clients allowed on the device or an interface. Only the allowed number of DHCP clients can obtain an IP address through the device or interface.
You can enable the device to check whether the MAC address in the Ethernet frame header matches the value of the CHADDR field in the DHCP message. If the two values match, the message is forwarded. Otherwise, the message is discarded.
Detecting Client Locations Through an LDRA
An LDRA-enabled device can record client location information and forward the information to the DHCPv6 server. The DHCPv6 server then assigns IP addresses, accounting policies, and access control policies to the clients based on the client location information.
In the following figure, users obtain IPv6 addresses through DHCPv6. The administrator wants to restrict the network access rights of the users on interface1 to improve network security.
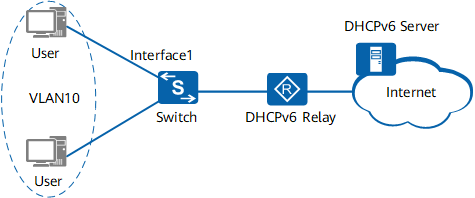
LDRA application
In the traditional process of allocating IPv6 addresses, the DHCPv6 server cannot obtain the physical locations of clients. Therefore, the server cannot assign specified IP addresses or policies to users on a certain interface.
To solve this issue, the administrator enables DHCP snooping and LDRA on the Switch. The Switch can then obtain the location information of clients and forward the information to the DHCPv6 server. The server assigns IP addresses and security policies to clients based on the client location information.
The LDRA function records only the client location information and forwards the information to the DHCPv6 server through Relay-Forward messages. The differentiated policies for IP address allocation, accounting, and access control are configured on the DHCPv6 server.
How Does DHCP Snooping Work?
DHCP snooping has two modes: DHCPv4 snooping and DHCPv6 snooping. Both modes function in a similar manner. This section uses DHCPv4 snooping as an example.
A DHCP snooping-enabled device forwards DHCP Request messages of users (DHCP clients) to an authorized DHCP server through the trusted interface. The device then generates DHCP snooping binding entries according to the DHCP ACK messages it receives from the DHCP server. To prevent attacks from unauthorized users, the device checks DHCP messages it receives through DHCP snooping-enabled interfaces against the binding table.
DHCP Snooping Trust Function
If a bogus DHCP server exists on a network, as shown in the following figure, DHCP clients may obtain incorrect IP addresses and network configuration parameters from it, leading to communication failures. The trust function controls the source of DHCP Reply messages to prevent bogus DHCP servers from assigning IP addresses and other configurations to DHCP clients.
DHCP snooping involves two interface roles: trusted interface and untrusted interface. The interface roles ensure that DHCP clients obtain IP addresses from an authorized DHCP server.
- DHCP ACK messages, NAK messages, and Offer messages are received from the trusted interface. In addition, the device only forwards DHCP Request messages from DHCP clients to the authorized DHCP server through the trusted interface.
- DHCP ACK messages, NAK messages, and Offer messages are discarded on untrusted interfaces.
When DHCP snooping is enabled on a Layer 2 access device, as shown in the following figure, the interface directly or indirectly connected to the authorized DHCP server is generally configured as a trusted interface (for example, if1). Other interfaces are configured as untrusted interfaces (for example, if2). To ensure that DHCP clients can obtain IP addresses only from the authorized DHCP server, the DHCP Request messages from DHCP clients are forwarded only through the trusted interface. Bogus DHCP servers cannot assign IP addresses to the DHCP clients.
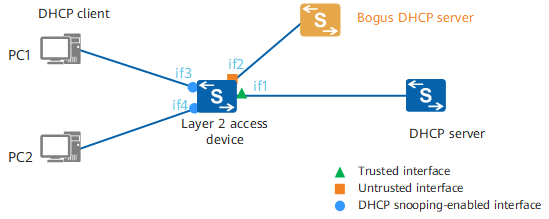
DHCP snooping trust
DHCP Snooping Binding Table
- A PC, functioning as a DHCP client, broadcasts a DHCP Request message.
- The DHCP snooping-enabled Layer 2 access device forwards the message to the DHCP server through the trusted interface.
- The DHCP server unicasts the DHCP ACK message carrying an IP address to the PC.
- The Layer 2 access device obtains required information, such as the PC's MAC address, IP address, and lease time of the IP address, from the DHCP ACK messages. It learns information (interface number and VLAN ID) about the DHCP snooping-enabled interface connected to the PC and generates a DHCP snooping binding entry for the PC.
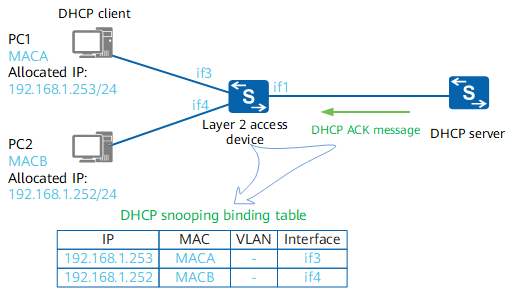
DHCP snooping binding table
A DHCP snooping binding entry is aged out when the IP address lease time expires. Alternatively, the entry is deleted when the client sends a DHCP Release message to release its IP address.
The DHCP snooping binding table records the mappings between IP addresses and MAC addresses of DHCP clients. The device can check DHCP messages against the DHCP snooping binding table to prevent attacks initiated by unauthorized users.
Configure DHCP snooping on the Layer 2 access devices or the first DHCP relay agent to ensure that the device obtains parameters such as MAC addresses for generating DHCP snooping binding entries.
If DHCP snooping is enabled on a DHCP relay agent, a trusted interface does not need to be configured on the DHCP relay agent. After receiving DHCP Request messages from clients, the DHCP relay agent modifies the source/destination IP addresses and MAC addresses, and unicasts the messages to the authorized DHCP server. Therefore, the DHCP ACK messages received by the DHCP relay agent are valid, and the DHCP snooping binding entries generated by the DHCP relay agent are correct.
- Author: Li jiyuan
- Updated on: 2021-09-30
- Views: 9590
- Average rating:






