What Is Opportunistic Wireless Encryption (OWE)?
OWE is a Wi-Fi Enhanced Open authentication mode, as a part of Wi-Fi Protected Access 3 (WPA3), which allows for network access without the password. In OWE mode, the Diffie-Hellman key exchange algorithm is used to encrypt data on the Wi-Fi network, thereby protecting data exchange between STAs and the Wi-Fi network.
What Problems Does OWE Solve?
Risks of Traditional Open Wi-Fi Networks
Nowadays, public Wi-Fi networks are available in various public venues, such as airports, stations, hotels, and stadiums. Most of these Wi-Fi networks adopt the open authentication mode to allow for user access anytime anywhere, without entering the password. Such open Wi-Fi networks, however, are vulnerable to unauthorized access of attackers. Additionally, as data exchanged between STAs and Wi-Fi networks is transparent and unencrypted, attackers may listen on the data transmission process and intercept user data.
Enhanced Open Wi-Fi Networks Using OWE Authentication
In 2018, the Wi-Fi Alliance released WPA3 — the next-generation Wi-Fi encryption protocol — to resolve the insecure data transmission issue caused by open authentication on Wi-Fi networks. WPA3 provides the Enhanced Open network authentication mode — OWE authentication — based on open system authentication.
OWE authentication makes Wi-Fi network access as convenient as that in open authentication mode, allowing users to access the Wi-Fi network without entering the password. In OWE authentication mode, a STA and an AP perform a Diffie-Hellman key exchange to encrypt data transmitted between the STA and Wi-Fi network, thereby protecting user data security.
OWE Authentication Process
Based on the open authentication process, OWE authentication adds a Diffie-Hellman key exchange process. The following compares these two authentication modes.
Open Authentication Process
When an AP uses open authentication, it allows all authentication requests from STAs. The following figure illustrates the specific authentication process.
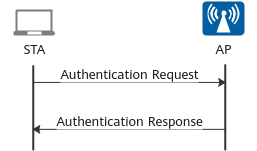
Open authentication process
- Authentication Request: The STA sends an Authentication Request to the AP.
- Authentication Response: The AP uses open authentication that allows all authentication requests and therefore returns the success authentication result to the STA.
OWE Authentication Process
When an AP uses OWE authentication, two phases are involved: OWE Discovery and OWE Association. The following figure illustrates the specific authentication process.
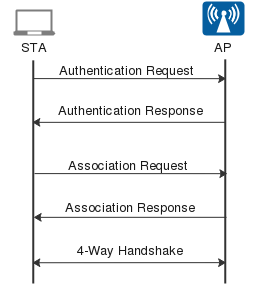
OWE authentication process
OWE Discovery phase:
- Authentication Request: The STA sends an Authentication Request to the AP.
- Authentication Response: After the STA succeeds in OWE authentication, the AP returns the authentication result to the STA. The authentication result contains the Authentication and Key Management (AKM) field, notifying the STA of its OWE authentication capability. After receiving the authentication result, the STA enters the OWE Association phase if it supports OWE authentication or accesses the network in open authentication mode if it does not support OWE authentication.
OWE Association phase:
- Association Request: The STA sends an Association Request to the AP, which contains the public key of the STA in the Diffie-Hellman Parameter element.
- Association Response: The AP returns the association result to the STA, which contains the public key of the AP in the Diffie-Hellman Parameter element. After the public key exchange between the STA and AP is completed, a pairwise master key (PMK) is generated.
- 4-Way Handshake: The STA and AP perform a 4-way handshake to determine the key used for communication.
OWE Transition Mode
The migration from an open Wi-Fi network to an enhanced open Wi-Fi network is completed step by step, while user devices are also gradually upgrading. For STAs that do not support OWE authentication, the OWE transition mode is available so that such STAs can access the network in open authentication mode. Meanwhile, the OWE transition mode allows OWE-capable STAs to access the network in OWE authentication mode. The OWE transition mode is implemented as follows:
- Two SSIDs are created on an AP, for example, SSID 1 for open authentication and SSID 2 for OWE authentication.
- SSID 1 is broadcast, and SSID 2 is hidden. Therefore, only SSID 1 is visible to STAs.
- SSID 1 carries an OWE Transition Mode element and SSID 2 information. When an OWE-capable STA connects to SSID 1, it is directly associated with SSID 2 in OWE transition mode.
- Author: Zhou Qiang
- Updated on: 2022-04-02
- Views: 15508
- Average rating: