What Is a Zero-Day Attack?
A zero-day vulnerability usually refers to a security vulnerability that has not been fixed because no patch is available. A zero-day attack exploits the zero-day vulnerability to target a system or application. Zero-day vulnerabilities are usually of high severity, so they are often very destructive. Currently, there is no security product or solution that can completely mitigate zero-day attacks. To effectively reduce the probability of being attacked by zero-day attacks and minimize the loss caused by such attacks, build a complete defense system and improve individuals' awareness of cyber security.
What Is a Zero-Day Vulnerability?
The number in "N-day" indicates the number of days after such a vulnerability is disclosed but no patch has been developed, which in the case of "zero-day" indicates that a patch is not developed the day such a vulnerability is disclosed. In most cases, a patch cannot be developed on the same day when a vulnerability is disclosed. If no patch is available after N days, it is called an N-day vulnerability. "Zero-day" can also refer to an attack that exploits such a vulnerability the day it is disclosed. This is called a zero-day attack.
"Zero-day" is no longer used to indicate how many days the vulnerability has existed as hackers may have discovered the vulnerability a long time ago but not yet disclosed it. Only when such a vulnerability is disclosed can it be detected by software vendors and the public and called a zero-day vulnerability. Therefore, "zero-day" often means the vulnerability is unknown to software vendors and the public but known to hackers or traders on the dark web.
How Does a Zero-Day Vulnerability Lead to a Zero-Day Attack?
Typically, when someone finds a potential security issue in a piece of software, he or she will notify the software supplier or release it to the public, and the software supplier will start to repair the vulnerability and develop a corresponding patch. If a hacker discovers a vulnerability, it takes time for him or her to develop malware. During this period, network administrators implement measures to mitigate the zero-day vulnerability, for example, disabling some services until a patch is released.
In most cases, hackers are the first to discover a zero-day vulnerability. Hackers usually use automated test tools and reverse engineering to search for such vulnerabilities. After discovering such a vulnerability, the hackers can exploit them to quickly and easily get round strict network protection measures, penetrate the network, and launch zero-day attacks. In short, a zero-day attack is a network attack that exploits a zero-day vulnerability to attack a system or software application.
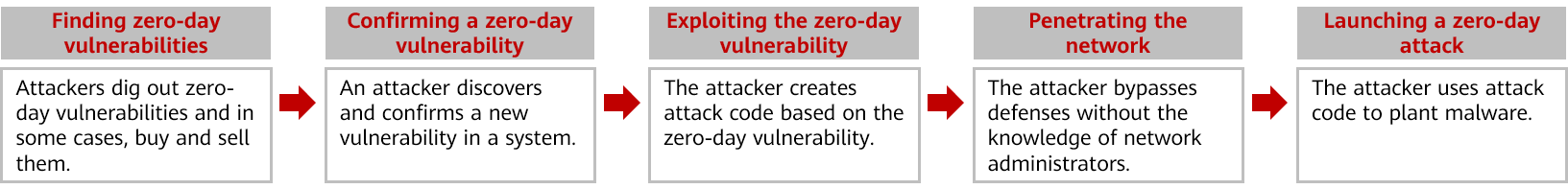
Process of a zero-day vulnerability leading to a zero-day attack
Common types of zero-day attacks are as follows:
- Account Takeover (ATO) Attack
In an ATO attack, an attacker uses malware to take unauthorized control over a compromised system and perform a series of malicious operations through the victim. For example, an attacker installs malware in a system, sends phishing messages or emails to the victim's contacts, or steals money from the victim's banking account.
- Watering Hole Attack
A watering hole attack is named after the way predators in the wild wait at the watering hole where many animals go to drink to find and attack their prey.
Similarly in the cyber world, attackers in the cyber world first analyze the websites frequently visited by target groups and then implant malicious programs into these websites. Then, when members of the target group visit these websites, they are highly susceptible to the malicious programs and then spread such programs to other members.
- Zero-Day Wednesday
Microsoft usually releases updates for system patches on the second Tuesday of every month. This is unofficially called "Patch Tuesday". However, if a vulnerability (such as a zero-day vulnerability) is discovered, Microsoft will release an emergency patch instead of waiting for the patch day. Some hackers choose to launch new attacks on the day after Patch Tuesday in an attempt to exploit the attack time window. Therefore, such attacks are called zero-day Wednesday attacks.
Nowadays, "Patch Tuesday" refers to the day when Microsoft, Adobe, and other software vendors periodically release patches. Hackers take advantage of the period between releases to launch attacks. Software vendors do not frequently release emergency patches for all vulnerabilities. That means hackers will have sufficient time to compromise the system.
Why Is a Zero-Day Attack Dangerous?
Zero-day vulnerabilities are usually of high severity, so they are often very destructive. Research shows that 30% of malware is based on zero-day vulnerabilities. The related forms of malware include viruses, worms, and Trojan horses. Zero-day attacks are generally designed to spread quickly to infect as many hosts and systems as possible. Zero-day attacks have evolved from passively and slowly spreading files and macro viruses to more proactive self-propagating email worms and hybrid threats, greatly shortening the threat propagation time and expanding the scope of impact.
If a zero-day attack occurs, software or security vendors usually need several days or even months to analyze attack information. Hackers can obviously obtain substantial benefits during this period.
Zero-day attacks are targeted at the following types of victims:
- High-Value Targets
Such targets include financial and healthcare institutions, government, and military agencies. Successful attacks on such targets would have huge economic or political implications. Zero-day vulnerabilities of such targets are often the most expensive on the dark web.
- Targets with a Large Impact Scope
Such targets include browser software, operating system software, common application software, and so on. According to statistics on zero-day vulnerabilities in recent years, the majority of attacks are launched against Microsoft software (such as Windows OS, Internet Explorer, and Office software). This is because Microsoft products are the most widely used.
Notable Zero-Day Attack Events
- Stuxnet
Stuxnet may be the first cyberweapon in the world that has ever been put into use. This malware exploited multiple zero-day vulnerabilities for penetration and spreading, eventually manipulating centrifuges to wreak destruction on them at an Iranian nuclear power plant.
- Sony Zero-Day Attack
The Sony zero-day attack targeted Sony Pictures. Hackers exploited a zero-day vulnerability to penetrate into Sony's network and quickly accessed all important information. Then, hackers began to release the stolen confidential information and files, including copies of new movies that had not yet been released, business transaction details, and business plans, which caused great losses to Sony.
- Operation Aurora
Operation Aurora is a typical APT attack. Hackers leveraged social engineering to investigate Google employees' information and then enticed these employees to click on malicious website links. By exploiting the zero-day vulnerability and implanting malware, the hackers finally attacked Google.
Methods Used to Reduce Zero-Day Attack Risks
Currently, there is no security product or solution that can completely mitigate zero-day attacks. To effectively reduce the probability of being attacked by zero-day attacks and minimize the loss caused by such attacks, build a complete defense system and improve individuals' awareness of cyber security.
The following measures can be taken to prevent zero-day attacks:
- Enhance employees' cyber security awareness: Organize cyber security training for all employees to master basic cyber security knowledge, and prevent hackers from initiating internal attacks.
- Reinforce computer systems: Computers are usually the weakest part of an entire network. Harden security of the terminal systems to effectively reduce zero-day attacks.
- Update software in real time: Common software, such as browsers, antivirus software, and office software, must be updated in real time.
- Promptly fix vulnerabilities: Periodically scan for vulnerabilities of network devices and promptly fix existing vulnerabilities to reduce attack risks.
- Strengthen the construction of network security facilities: Deploy the necessary security devices and software (such as the big data security analysis system, NGFW, vulnerability scanning device, and antivirus software) on the network to reduce the impact scope and severity of zero-day attacks.
- Enhance permission authentication and review: Implement the zero-trust security solution to enhance user operation authorization and user identity review.
- Work out an emergency response solution: As the threats of zero-day attacks cannot be completely eliminated, the emergency response solution helps enterprises quickly prevent attacks and minimize losses.
How Does Huawei Help You Defend Against Zero-Day Attacks?
In most cases, it is difficult to discover or detect zero-day vulnerabilities in advance. Unlike hackers who launch zero-day attacks, others can confirm that such attacks are initiated by exploiting zero-day vulnerabilities only after obtaining detailed information about the attacks. The only way to eliminate zero-day vulnerabilities is to ask software vendors to provide patches, usually taking a long time. Therefore, software vendors usually provide functions to prevent zero-day attacks in the latest patches. Actually, this method does not completely resolve such vulnerabilities.
To adapt to increasingly complex network environments and cope with advanced threats (such as APTs), Huawei provides various security solutions and products to help you promptly detect security risks and reduce related impact.
- Anti-APT and Big Data Security Solution effectively prevents APT attacks from threatening enterprises' core information assets and implements various functions, such as threat detection, threat source tracing, evidence collection, and network-wide collaborative defense. This solution applies to scenarios such as finance, government, energy, and Internet enterprises.
- HiSec Insight Advanced Threat Analytics System
The HiSec Insight uses big data technology and intelligent detection algorithms to perform multi-dimensional relation analysis on mass data, detect various threat events in real time, and restore the entire APT kill chain model. In addition, it displays the security situation of an entire network to provide users with an overview of the network security status.
The HiSec Insight supports behavior analysis technologies. By comparing differences between individual behaviors and standard behavior patterns, the HiSec Insight can detect signs of zero-day attacks in advance.
- FireHunter6000 Series Sandbox
The FireHunter can accurately identify unknown malicious file penetration and C&C-based malicious external connections. By restoring file data from network traffic and analyzing them in a virtual environment, the FireHunter can detect and defend against unknown malicious files.
- USG6000E Firewall
In addition to providing NGFW capabilities, the USG6000E can interwork with other security devices to enhance border detection capabilities and effectively mitigate advanced threats. The USG6000E also supports heuristic detection (signature analysis technology). It leverages machine learning to analyze suspicious features in files and dig out potential malware. It then automatically generates new signatures for subsequent zero-day vulnerability detection.
Related Concepts
What Are Zero-Day Markets?
A dozen years ago, zero-day vulnerabilities were rare. There may be only a few pieces of malware related to zero-day vulnerabilities among millions. Zero-day attacks at that time were often easy to launch, such as implementing remote intrusions or gaining control.
However, as cyber security technologies continuously improve, it is almost impossible to break through defense systems by exploiting a zero-day vulnerability alone, not to mention obtaining control. In fact, to launch an APT attack, several or even dozens of zero-day vulnerabilities must be collectively exploited in a combo attack to break through the defense system of a victim. It is common that high-value zero-day vulnerabilities sell at sky-high prices, which is an important driving force for zero-day markets.
Zero-day markets are classified into the following types:
- Black market: Buyers mainly exploit zero-day vulnerabilities to commit crimes, such as intruding systems, stealing passwords, and transferring money. The black market usually exists on the dark web.
- White market: mainly covers bug bounty programs, for example, Zero Day Initiative (ZDI), created by institutions or vendors. Vulnerability finders (possibly hackers) disclose vulnerability information to software suppliers and are rewarded bonuses. In turn, the software suppliers will release patches as soon as possible before zero-day attacks are initiated. Special buyers in this market are security companies, which use zero-day vulnerabilities for penetration testing to determine how effectively a client system can defend against attacks.
- Gray market: Buyers are mainly military, intelligence agencies, and law enforcement departments, which exploit zero-day vulnerabilities for political or surveillance purposes.
The prices of zero-day vulnerabilities may vary greatly depending on many factors, such as how much benefit a vulnerability can bring. In most cases, vulnerabilities applicable to multiple versions are more valuable than those that apply to a single version, and iOS vulnerabilities are more valuable than Microsoft vulnerabilities.
What Is the Dark Web?
The dark web is a network that cannot be found using routine search methods (such as Google Chrome). Generally, special software or host authorization is required to access a specific dark web. Statistics show that domain names of dark webs outnumber those of visible networks by hundreds of times.
For a dark web with high anonymity, many illicit activities are carried out, such as drug dealing, arms trafficking, illegal pornography sharing, and hacking services. Many hackers will not exploit zero-day vulnerabilities they have discovered, but sell them on the dark web. High-value zero-day vulnerabilities can be sold for millions of dollars.
- Author: Yan Guanghui
- Updated on: 2021-09-30
- Views: 7481
- Average rating: